MCP Server Ecosystem Reference 2026
First Published:
Last Updated:
* The contents of this article reflect the state as of the Last Updated date shown above. The MCP ecosystem moves quickly; rows are revised in place as servers ship, are archived, or change transports.
The Model Context Protocol (MCP) crossed the boundary from "interesting open standard" to "default integration layer for agent runtimes" during 2025 and 2026. As of 2026, every major LLM host - Claude Desktop, Claude Code, Cursor, Codex CLI, the ChatGPT desktop app, the OpenAI Agents SDK, and Amazon Bedrock AgentCore Gateway - speaks MCP natively, and the catalog of public MCP servers has grown from a single GitHub README into a tiered ecosystem of reference implementations, vendor-operated remote servers, and a long tail of community packages.This article is a Reference Aggregation Page that answers two operational questions in one place: "what MCP servers actually exist as of 2026?" and "which transports and authentication modes do they support?" It is refreshed in place as needed within the publication year; each row is a self-contained pointer to its upstream source of truth rather than a usage tutorial. For the deeper end-to-end pattern of building and shipping an MCP server on AWS Lambda, see the companion article MCP Server on AWS Lambda Complete Guide. For the runtimes that consume these servers in production, see Amazon Bedrock AgentCore Implementation Guide Part 1: Runtime, Memory, and Code Interpreter Patterns and Amazon Bedrock AgentCore Implementation Guide Part 4: Multi-Agent Orchestration. For the host side, see Claude Code Getting Started Guide and Claude Code Harness and Environment Engineering Guide.
This snapshot is refreshed as needed within the publication year. Last reviewed: 2026-05. Any value in a row that depends on upstream vendor pages can drift between refreshes; entries flagged with a footnote directly beneath the relevant table are the ones whose upstream is most likely to have changed since this revision was compiled.
1. How This Reference Was Compiled
A snapshot is only useful if the reader can audit how it was built. This section documents the upstream sources, the inclusion bar, the refresh cadence, and what this article deliberately does not cover.1.1 Sources of Truth
Three classes of upstream were treated as authoritative. Anything else - blog roundups, awesome-lists, social posts - was treated as derivative and not used as a primary source.- Protocol: modelcontextprotocol.io/specification for the current revision (2025-11-25, the first-anniversary release) and the dated revision pages for historical context (2024-11-05, 2025-03-26, 2025-06-18).
- Reference servers: the modelcontextprotocol/servers GitHub repository for what counts as a reference implementation, including the archive notices and pointers to maintained forks.
- Vendor-operated servers: each vendor's own product page or repository - AWS (awslabs.github.io/mcp), Anthropic (docs.claude.com/en/docs/agents-and-tools/mcp), GitHub (github/github-mcp-server), Cloudflare, Stripe, Atlassian, Notion, Linear, Asana, Sentry, Microsoft (Azure MCP), Vercel, Supabase, and others - as the source of truth for transports, license, authentication, and supported spec revision.
For community servers a single canonical repository was used; abandoned forks and republished mirrors were ignored.
1.2 Inclusion Criteria
A server was included in this reference if at least one of the following held:- It is one of the reference implementations under
modelcontextprotocol/servers(active or archived). - It is operated or maintained by a recognized vendor whose primary product the MCP server exposes (the list in §1.1).
- It is a community-maintained server with sustained activity in 2026 (commits within the last 90 days), at least one transport that matches the 2025-03-26, 2025-06-18, or 2025-11-25 spec, and clear practical coverage of a category that is not already represented by a reference or vendor entry.
This is deliberately not a complete index of every public MCP server. The long tail of single-purpose community packages is intentionally omitted so the page stays useful as a reference instead of decaying into a directory listing. When a category contains more than a few credible community servers, the most actively maintained one was chosen and the rest are linked from its repository's README, not duplicated here.
1.3 Refresh Cadence
This article is refreshed in place as needed within the publication year. The URL slug is stable -mcp_server_ecosystem_reference_2026 - but the content evolves. Sections most prone to drift are concentrated in two places to make diffs against the prior refresh easy to read:- Recent Additions (§7) - servers that became generally available, joined the reference set, or moved from preview to stable in the last 90 days.
- Recent Deprecations (§8) - servers archived, marked end-of-life, or absorbed into a successor since the last refresh.
Refreshes within the publication year overwrite this page in place. The first review of this 2026 edition was completed on 2026-05; subsequent refreshes carry the same URL.
1.4 What This Reference Is Not
Three things are deliberately out of scope to keep this page tractable:- Not a performance benchmark. Tool-call latency, cold start figures, JSON-RPC framing overhead, and Streamable HTTP throughput belong in a separate dedicated benchmark article.
- Not a per-server usage guide. Each server has at most one official docs link in its row. Setup instructions, CLI commands, and config snippets are intentionally not duplicated here - the upstream README is authoritative and any duplication here would rot between refreshes.
- Not a pricing comparison. Vendor-operated remote MCP servers may have free and paid tiers, but pricing is published on vendor pricing pages and changes more often than this snapshot refreshes.
2. MCP Protocol Quick Reference
Before reading the catalog tables, a short refresher on the protocol shape is useful. MCP is JSON-RPC 2.0 over a configurable transport, with a small set of primitives that hosts and servers negotiate at connect time. This section is a Quick Reference; for the end-to-end mechanics of building a server against the current spec, see the companion article MCP Server on AWS Lambda Complete Guide, and the companion MCP Server Implementation Reference for a vendor-by-vendor comparison pinned to2025-11-25.2.1 Spec Revisions Timeline
Four spec revisions are relevant in 2026. The current revision is2025-11-25, the first-anniversary release. Most production servers still target 2025-06-18 or 2025-03-26 while migrations to 2025-11-25 roll out; hosts negotiate downward gracefully but reject the original pre-2025-03-26 transports for new connections.* You can sort the table by clicking on the column name.
| Revision | Released | Key Additions |
|---|---|---|
| 2024-11-05 | 2024-11-05 | Initial public spec. JSON-RPC 2.0 base; HTTP+SSE transport; tools/list, resources/list, prompts/list primitives. |
| 2025-03-26 | 2025-03-26 | Streamable HTTP transport (supersedes HTTP+SSE); tool annotations including readOnlyHint and destructiveHint; resource subscriptions. |
| 2025-06-18 | 2025-06-18 | OAuth 2.1 hardening: RFC 9728 Protected Resource Metadata; RFC 8707 audience binding (Resource Indicators); elicitation primitive; structured tool output schemas and resource links in tool results; MCP-Protocol-Version header required on subsequent HTTP requests; JSON-RPC batching support removed. |
| 2025-11-25 | 2025-11-25 | First-anniversary release and current spec. Schema split into a dedicated schema.ts per revision under the modelcontextprotocol/specification repository; documentation reorganized at modelcontextprotocol.io/specification/2025-11-25/. Hosts and servers continue to negotiate the wire version via the MCP-Protocol-Version header; servers that do not understand a client's requested version must return HTTP 400. |
2.2 Primitives
MCP exposes three core primitives plus four optional capabilities that hosts can advertise to participating servers.- Core primitives
- Tools - functions the model can invoke (
tools/list,tools/call). - Resources - read-only data the host can fetch or subscribe to (
resources/list,resources/read,resources/subscribe). - Prompts - reusable, server-provided prompt templates (
prompts/list,prompts/get).
- Tools - functions the model can invoke (
- Optional capabilities
- Sampling - the server asks the host to run a model completion on its behalf.
- Roots - the host advertises trusted filesystem roots and notifies the server of changes.
- Elicitation - the server requests user-side structured input (introduced in 2025-06-18).
- Logging - the server emits structured log notifications that surface in the host's UI.
The majority of community servers implement Tools only. Reference and vendor servers increasingly implement Tools + Resources, with Prompts and the optional capabilities still uncommon.
2.3 Transports
Three transports are recognized as of 2026, with one (WebSocket) still outside the core spec.- stdio - the host launches the server as a subprocess and exchanges JSON-RPC frames over its standard streams. The default for local servers in Claude Desktop, Claude Code, and Cursor.
- Streamable HTTP - a single HTTPS endpoint accepts
POSTfor JSON-RPC requests andGETfor an optional Server-Sent Events stream. The default for remote and multi-tenant servers as of 2025-03-26; it replaced the older HTTP+SSE transport. AnMcp-Session-Idresponse header lets the server opt into stateful sessions; stateless servers (the recommended default on AWS Lambda) simply omit it. - WebSocket - bidirectional frames. Not yet covered by the official spec but used by a small number of community servers for long-lived agent sessions. Marked
[Preview]throughout this reference.
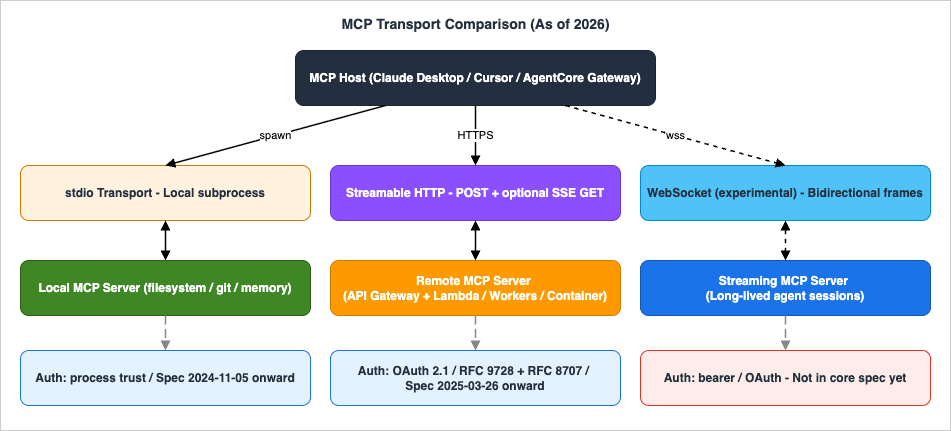
2.4 OAuth 2.1 and Protected Resource Metadata
Remote MCP servers in 2026 are expected to publish RFC 9728 Protected Resource Metadata at a discoverable URL and to enforce RFC 8707 audience binding so that an access token issued for one MCP server cannot be replayed at another. Servers that comply fully are flaggedAuth: OAuth 2.1 in the catalog tables. Older servers that authenticate with a long-lived bearer token are flagged Auth: API Key. Locally launched stdio servers that rely on the host's process trust are flagged Auth: None (local). AWS-native servers that authenticate via the caller's IAM identity (SigV4) are flagged Auth: IAM SigV4.The Cloudflare-hosted "remote MCP" pattern - Workers-backed servers exposed through a public OAuth-protected endpoint - has become the de facto reference for vendor-operated multi-tenant servers in 2026, with Stripe, Linear, Asana, and Sentry all converging on a similar shape.
3. Reference Servers by Category
The catalog is organized into four buckets - reference (§4), vendor-operated (§5), community (§6), and refresh-over-refresh delta (§7 and §8). Every table in those sections shares the same column layout, defined in §3.2.3.1 Index
Jump to a bucket:- §4 Official Reference Implementations
- §5 Vendor-Operated Servers - AWS, Anthropic and First-Party, GitHub / Cloudflare / Stripe, Atlassian / Notion / Linear / Asana / Sentry, Microsoft / Google, Supabase / Vercel and other infra
- §6 Community Servers by Category - Developer Tools, Search and Knowledge, Database and Data, Observability, Productivity and Communication
- §7 Recent Additions
- §8 Recent Deprecations
- §9 Frequently Asked Questions
- §10 References
3.2 Reading the Tables
Every catalog table in this reference uses the same eight columns.| Column | Meaning |
|---|---|
| Server | Server name, linked to the source of truth (upstream repo or vendor docs). |
| Maintainer | The org or individual that operates the server and accepts issues. |
| Language | Primary implementation language. |
| License | SPDX-style license identifier or Proprietary for vendor-only services. |
| Transports | stdio / Streamable HTTP / stdio+HTTP / WebSocket. |
| Auth | None (local) / None (public) / OAuth 2.1 / API Key / IAM SigV4 / DB credentials / kubeconfig (definitions below). |
| Status | Stability badge (legend below). |
| Spec Rev | MCP spec revision the server targets. |
Status badge legend:
[Stable]- production-grade. No breaking changes in the last 90 days; vendor or maintainer commits to a deprecation window.[Beta]- feature-complete but evolving. Expect minor breaking changes between releases.[Preview]- early access. May not implement all primitives or all transports.[Deprecating YYYY]or[Deprecating YYYY-MM]- announced end-of-life. The month is included when the vendor has published a specific cut-off date; year-only is used when only the year is publicly announced. Successor (if any) is noted in §8.
Auth value legend:
None (local)- the server runs as a stdio subprocess and inherits the host user's privileges; no transport-level authentication.None (public)- a Streamable HTTP server intentionally exposed without authentication because it serves only public read-only data (e.g.aws-knowledge-mcp-server).OAuth 2.1- RFC 9728 Protected Resource Metadata published, RFC 8707 audience binding enforced. See §2.4.API Key- a long-lived bearer token (vendor-issued or user-issued) passed as an HTTP header or environment variable.IAM SigV4- the caller's AWS credentials sign each request; permissions are governed by the caller's IAM identity rather than by the server.DB credentials- a database connection string (username/password or a DSN) is supplied at server start time; the MCP server itself is unauthenticated and trusts whoever can reach it on stdio.kubeconfig- the server reads a local kubeconfig file at start time and inherits its cluster credentials; no MCP-level authentication.
Cells whose upstream value the author could not verify against vendor docs at the time of this snapshot are flagged with a footnote directly beneath the table. These are the ones to double-check before depending on the value in production.
3.3 Category Buckets
The catalog uses twelve practical categories. Each category appears in exactly one of §4 (reference), §5 (vendor-operated), or §6 (community), depending on where the most authoritative current implementation lives - so the same product domain (e.g. Database) shows up underaurora-postgres-mcp-server in §5.1 and under postgres-mcp in §6.3 without being split across both.- Filesystem and Local IO — covered in §4 (reference
filesystem). - Web / Fetch / Browser — covered in §4 (reference
fetch) and §6.1 (playwright-mcp). - Database — covered in §5.1 (AWS Labs Aurora / DynamoDB) and §6.3 (Postgres, MongoDB, ClickHouse, Redis, Elasticsearch, Snowflake).
- Search and Knowledge — covered in §5.1 (
aws-knowledge-mcp-server) and §6.2 (Exa, Tavily, Perplexity, Brave). - Developer Tools (Git, CI, Build, Containers, Kubernetes, Terraform) — covered in §4 (reference
git), §5.3 (GitHub) and §6.1 (Playwright, Kubernetes, Docker, Terraform, shell, Jupyter). - Productivity (Calendar, Mail, Docs, Notes) — covered in §5.4 (Notion) and §6.5 (Todoist, Gmail, Google Calendar).
- Communication (Chat, Notification) — covered in §6.5 (Slack, Discord).
- AWS-native — covered in §5.1.
- GCP-native — covered in §5.5 (community
google_workspace_mcpafter Google's first-party repos were archived). - Azure-native — covered in §5.5 (consolidated
microsoft/mcpcatalog). - Observability and Security — covered in §5.4 (Sentry) and §6.4 (Grafana, Loki, Prometheus).
- Payments and Commerce — covered in §5.3 (Stripe).
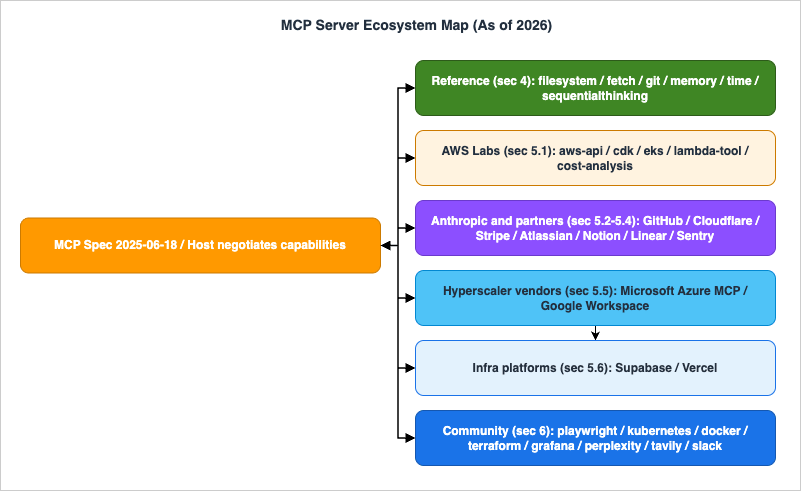
4. Official Reference Implementations
The modelcontextprotocol/servers repository is the canonical answer to "what should an MCP server look like?" As of 2026 most of the original first-party reference servers were archived during 2025 and migrated to vendor or community ownership, leaving a smaller curated set in the upstream repo plus explicit pointers to maintained forks. The archived rows live in §8 Recent Deprecations together with their successor links.* You can sort the table by clicking on the column name.
| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| filesystem | MCP Project | TypeScript | MIT | stdio | None (local) | [Stable] | 2025-06-18 |
| fetch | MCP Project | Python | MIT | stdio | None (local) | [Stable] | 2025-06-18 |
| git | MCP Project | Python | MIT | stdio | None (local) | [Stable] | 2025-06-18 |
| memory | MCP Project | TypeScript | MIT | stdio | None (local) | [Stable] | 2025-06-18 |
| time | MCP Project | Python | MIT | stdio | None (local) | [Stable] | 2025-06-18 |
| sequentialthinking | MCP Project | TypeScript | MIT | stdio | None (local) | [Stable] | 2025-06-18 |
| everything | MCP Project | TypeScript | MIT | stdio+HTTP | None (local) | [Stable] | 2025-06-18 |
The
everything server is intentionally not for production use - it is a test server that exercises every primitive and capability the spec defines, used by host implementers to validate their client. The memory server provides a minimal in-memory key/value store and a knowledge-graph variant; production agents that need persistence usually pair MCP with a host-managed store (Bedrock AgentCore Memory, OpenAI Memory) instead of relying on this reference implementation.5. Vendor-Operated Servers
This is the section that has grown the fastest between 2025 and 2026. Vendor-operated servers - servers that the product vendor itself runs (or publishes as a first-party install) - have a noticeably different operational shape from the reference set: most areStreamable HTTP, most use OAuth 2.1, and most map one-to-one onto an existing product's API surface.5.1 AWS
AWS Labs publishes a coordinated catalog of MCP servers at awslabs.github.io/mcp. The list below is the most operationally relevant subset as of 2026; the upstream catalog page is authoritative for the complete inventory. All AWS Labs servers can run as stdio local servers and most also expose a Streamable HTTP variant suitable for hosting in AWS Lambda (see MCP Server on AWS Lambda Complete Guide) or as an AgentCore Gateway target.* You can sort the table by clicking on the column name.
| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| aws-api-mcp-server | AWS Labs | Python | Apache-2.0 | stdio+HTTP | IAM SigV4 | [Stable] | 2025-06-18 |
| aws-knowledge-mcp-server | AWS Labs | Python | Apache-2.0 | Streamable HTTP | None (public) | [Stable] | 2025-06-18 |
| cost-analysis-mcp-server | AWS Labs | Python | Apache-2.0 | stdio+HTTP | IAM SigV4 | [Stable] | 2025-06-18 |
| cdk-mcp-server | AWS Labs | Python | Apache-2.0 | stdio | IAM SigV4 | [Stable] | 2025-06-18 |
| cloudformation-mcp-server | AWS Labs | Python | Apache-2.0 | stdio+HTTP | IAM SigV4 | [Stable] | 2025-06-18 |
| eks-mcp-server | AWS Labs | Python | Apache-2.0 | stdio | IAM SigV4 | [Stable] | 2025-06-18 |
| lambda-tool-mcp-server | AWS Labs | Python | Apache-2.0 | stdio+HTTP | IAM SigV4 | [Stable] | 2025-06-18 |
| bedrock-kb-retrieval-mcp-server | AWS Labs | Python | Apache-2.0 | stdio+HTTP | IAM SigV4 | [Stable] | 2025-06-18 |
| aurora-postgres-mcp-server | AWS Labs | Python | Apache-2.0 | stdio | IAM SigV4 | [Stable] | 2025-06-18 |
| dynamodb-mcp-server | AWS Labs | Python | Apache-2.0 | stdio | IAM SigV4 | [Stable] | 2025-06-18 |
| Amazon Bedrock AgentCore Gateway | AWS | (managed) | Proprietary | Streamable HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
AgentCore Gateway is a special case. It is not itself a server in the sense of a Tools provider - it is a translation layer that fans existing MCP servers (or REST APIs, Lambda functions, Smithy models, OpenAPI specs) out to any number of agents over a single Streamable HTTP endpoint with OAuth 2.1 authorization on the front and IAM-scoped access on the back. The Gateway pattern is the recommended way to expose internal AWS workloads to AgentCore Runtime agents, and is covered end-to-end in AgentCore Implementation Guide Part 4.
5.2 Anthropic and First-Party Integrations
Anthropic's role in the ecosystem is twofold: they author the spec, and they ship a set of first-party connectors that Claude Desktop's "Connectors" UI installs with one click. The list below is the catalog state as of 2026; Claude Desktop's settings UI is authoritative for the current shipping set.* You can sort the table by clicking on the column name.
| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| Claude Desktop bundled MCP servers | Anthropic | (various) | (various) | stdio | None (local) | [Stable] | 2025-06-18 |
| Claude Desktop Custom Connectors (OAuth) | Anthropic | (host feature) | Proprietary | Streamable HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
| Anthropic Messages API MCP support | Anthropic | (API feature) | Proprietary | Streamable HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
The Messages API MCP feature lets a client call an external Streamable HTTP MCP server inline with a Messages request, with Anthropic acting as the MCP client on behalf of the application. This is the canonical way to add MCP-mediated tools to a Claude API integration without running an in-process MCP client.
5.3 GitHub / Cloudflare / Stripe
Three platforms whose MCP servers are the most cited examples of "remote OAuth-protected MCP done right" in 2026.* You can sort the table by clicking on the column name.
| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| GitHub MCP Server | GitHub | Go | MIT | stdio+HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
| Cloudflare MCP Server | Cloudflare | TypeScript | Apache-2.0 | Streamable HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
| Cloudflare Workers Remote MCP | Cloudflare | (framework) | BSD-3-Clause | Streamable HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
| Stripe Agent Toolkit MCP | Stripe | TypeScript | MIT | stdio+HTTP | API Key | [Stable] | 2025-06-18 |
| Stripe Hosted MCP | Stripe | (managed) | Proprietary | Streamable HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
The GitHub MCP Server replaced the original community
modelcontextprotocol/servers/github reference in late 2025 and is now the canonical way to access repositories, issues, pull requests, Actions, and Code Search from Claude Code, Cursor, and AgentCore. The Cloudflare Workers Remote MCP pattern is a framework rather than a single server - it gives developers a one-file template for shipping their own OAuth-protected MCP server on Workers, and is what powers many of the SaaS-vendor servers listed in §5.4.5.4 Atlassian / Notion / Linear / Asana / Sentry
The SaaS-vendor cluster. All five converged on the Cloudflare-style remote OAuth pattern during 2025-2026.* You can sort the table by clicking on the column name.
| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| Atlassian Remote MCP Server | Atlassian | (managed) | Proprietary | Streamable HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
| Notion MCP Server | Notion | (managed) | Proprietary | Streamable HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
| Linear MCP Server | Linear | (managed) | Proprietary | Streamable HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
| Asana MCP Server | Asana | (managed) | Proprietary | Streamable HTTP | OAuth 2.1 | [Beta] | 2025-06-18 |
| Sentry MCP Server | Sentry | TypeScript | FSL-1.1-Apache-2.0 | stdio+HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
What makes this cluster useful as a reference is its uniformity. All five vendors converged on the same shape - Streamable HTTP transport, OAuth 2.1 with audience binding, managed hosting on either Cloudflare Workers or an equivalent edge runtime, and a one-click install path in Claude Desktop's Custom Connectors UI. If you are designing an MCP server for a SaaS product in 2026, this cluster is the canonical reference architecture to copy from before deviating.
5.5 Microsoft / Google
The two hyperscalers that are not AWS. Microsoft consolidated its servers into a single broad catalog repository during 2025-2026 (the earlierAzure/azure-mcp repository was archived in 2026-02 and migrated into microsoft/mcp under Azure.Mcp.Server; see §8). Google does not currently publish a first-party Workspace MCP server - Google's own googleworkspace/dev-assist and googleworkspace/developer-mcp repositories were archived in late 2025, so the community-maintained taylorwilsdon/google_workspace_mcp is the canonical entry that covers Drive, Calendar, Gmail, Docs, Sheets, Slides, Chat, Forms, Tasks, and Search behind a single OAuth flow.* You can sort the table by clicking on the column name.
| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| Microsoft MCP catalog | Microsoft | (various) | MIT | stdio+HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
| Microsoft Dev Box MCP (@microsoft/devbox-mcp) | Microsoft | TypeScript | MIT | stdio | OAuth 2.1 | [Beta] | 2025-06-18 |
| Google Workspace MCP (community) | Community (taylorwilsdon) | Python | MIT | stdio+HTTP | OAuth 2.1 | [Beta] | 2025-06-18 |
The community
google_workspace_mcp package exposes Google's product-specific surfaces (Drive, Calendar, Gmail, Docs, Sheets, Slides, Chat, Forms, Tasks, Search) behind a single OAuth flow rather than as separate one-product servers. The canonical non-Anthropic, non-AWS MCP host on the Google side - Gemini CLI - is excluded from this server catalog because it consumes MCP servers rather than exposing tools; treat it as a Google-side analog to Claude Code and Cursor.5.6 Supabase / Vercel and Other Infrastructure
Application infrastructure vendors that ship MCP servers for their own developer surfaces.* You can sort the table by clicking on the column name.
| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| Supabase MCP Server | Supabase | TypeScript | Apache-2.0 | stdio+HTTP | API Key | [Stable] | 2025-06-18 |
| Vercel MCP Server | Vercel | (managed) | Proprietary | Streamable HTTP | OAuth 2.1 | [Stable] | 2025-06-18 |
| Neon MCP Server | Neon | TypeScript | Apache-2.0 | stdio+HTTP | API Key | [Stable] | 2025-06-18 |
| Upstash MCP Server | Upstash | TypeScript | Apache-2.0 | stdio+HTTP | API Key | [Stable] | 2025-06-18 |
| PostHog MCP Server | PostHog | TypeScript | MIT | stdio+HTTP | API Key | [Beta] | 2025-06-18 |
The split between API-Key and OAuth 2.1 in this cluster tracks the underlying product surface. Vendors whose primary surface is already a developer-issued API key (Supabase, Neon, Upstash, PostHog) ship MCP servers that reuse the same key. Vendors whose surface is account-scoped end-user data (Vercel deployments tied to a Vercel account) layer OAuth 2.1 on top. Pick the auth mode that matches the underlying product rather than treating it as a free-floating MCP design choice.
6. Community Servers by Category
Community servers fill the gaps the reference and vendor sets leave open. The selection below is the actively maintained, category-representative top of each bucket as of 2026; the long tail (single-use forks, archived projects, hobbyist experiments) is intentionally not included.6.1 Developer Tools
* You can sort the table by clicking on the column name.| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| playwright-mcp | Microsoft (Playwright) | TypeScript | Apache-2.0 | stdio+HTTP | None (local) | [Stable] | 2025-06-18 |
| mcp-server-kubernetes | Community (Flux159) | TypeScript | MIT | stdio | kubeconfig | [Stable] | 2025-06-18 |
| docker-mcp | Community (QuantGeekDev) | Python | MIT | stdio | None (local) | [Beta] | 2025-06-18 |
| terraform-mcp-server | HashiCorp | Go | MPL-2.0 | stdio+HTTP | None (local) | [Stable] | 2025-06-18 |
| mcp-shell-server | Community (sooperset) | Python | MIT | stdio | None (local) | [Beta] | 2025-06-18 |
| jupyter-mcp-server | Datalayer | Python | BSD-3-Clause | stdio+HTTP | API Key | [Beta] | 2025-06-18 |
The shell-server pattern (
mcp-shell-server and several near-equivalents) is one of the most powerful and most dangerous community categories. Treat it like a remote-exec endpoint: only configure it in hosts whose process model isolates the resulting subprocesses, and never expose it remotely without OAuth audience binding and per-call tool annotations.6.2 Search and Knowledge
* You can sort the table by clicking on the column name.| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| exa-mcp-server | Exa Labs | TypeScript | MIT | stdio+HTTP | API Key | [Stable] | 2025-06-18 |
| tavily-mcp | Tavily | TypeScript | MIT | stdio+HTTP | API Key | [Stable] | 2025-06-18 |
| perplexity-mcp | Perplexity | TypeScript | MIT | stdio+HTTP | API Key | [Beta] | 2025-06-18 |
| brave-search-mcp-server | Brave | TypeScript | MIT | stdio+HTTP | API Key | [Stable] | 2025-06-18 |
6.3 Database and Data
* You can sort the table by clicking on the column name.| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| postgres-mcp (Crystal DBA) | Crystal DBA | Python | MIT | stdio+HTTP | DB credentials | [Stable] | 2025-06-18 |
| mcp-mongo-server | Community (kiliczsh) | TypeScript | MIT | stdio | DB credentials | [Beta] | 2025-06-18 |
| mcp-clickhouse | ClickHouse | Python | Apache-2.0 | stdio+HTTP | DB credentials | [Stable] | 2025-06-18 |
| mcp-server-elasticsearch | Elastic | TypeScript | Apache-2.0 | stdio+HTTP | API Key | [Deprecating 2026] | 2025-06-18 |
| mcp-redis | Redis | Python | MIT | stdio+HTTP | DB credentials | [Stable] | 2025-06-18 |
| Snowflake-Labs/mcp | Snowflake Labs | Python | Apache-2.0 | stdio+HTTP | OAuth 2.1 | [Beta] | 2025-06-18 |
6.4 Observability and Security
* You can sort the table by clicking on the column name.| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| mcp-grafana | Grafana Labs | Go | Apache-2.0 | stdio+HTTP | API Key | [Stable] | 2025-06-18 |
| loki-mcp | Grafana Labs | Go | MIT | stdio | API Key | [Beta] | 2025-06-18 |
| prometheus-mcp-server | Community (pab1it0) | Python | MIT | stdio | None (local) | [Beta] | 2025-06-18 |
6.5 Productivity and Communication
* You can sort the table by clicking on the column name.| Server | Maintainer | Language | License | Transports | Auth | Status | Spec Rev |
|---|---|---|---|---|---|---|---|
| todoist-mcp-server | Community (abhiz123) | TypeScript | MIT | stdio | API Key | [Beta] | 2025-06-18 |
| Gmail MCP Server | Community (GongRzhe) | TypeScript | MIT | stdio | OAuth 2.1 | [Beta] | 2025-06-18 |
| google-calendar-mcp | Community (v-3) | TypeScript | MIT | stdio | OAuth 2.1 | [Beta] | 2025-06-18 |
| slack-mcp-server (community) | Community (zencoderai) | TypeScript | Apache-2.0 | stdio+HTTP | OAuth 2.1 | [Beta] | 2025-06-18 |
| mcp-discord | Community (sooperset) | Python | MIT | stdio | API Key | [Preview] | 2025-03-26 |
7. Recent Additions
Servers that became generally available, joined a maintained vendor catalog, or moved from preview to stable in the rolling window ending at the Last reviewed date.* You can sort the table by clicking on the column name.
| Server | Change | What's new |
|---|---|---|
| Atlassian Remote MCP Server | Preview → Stable | OAuth 2.1 compliance audit completed; Jira Service Management endpoints added; published in Claude Desktop's connector catalog. |
| Asana MCP Server | New (Beta) | First-party Streamable HTTP server; replaces a community Asana MCP that has been archived (see §8). |
| Notion MCP Server | Beta → Stable | Database-write tool annotations now expose destructiveHint; OAuth 2.1 audience binding enforced. |
| terraform-mcp-server | Beta → Stable | Plan/Apply tools land with destructiveHint=true; new tfstate resource type. |
| aurora-postgres-mcp-server | New | AWS Labs ships a Postgres-on-Aurora MCP server distinct from the community postgres-mcp; IAM-SigV4 authentication. |
| Google Workspace MCP (community) | New (Beta) | The community-maintained taylorwilsdon/google_workspace_mcp emerged as the de facto Workspace MCP after Google's own googleworkspace/dev-assist and googleworkspace/developer-mcp were archived; covers Drive, Calendar, Gmail, Docs, Sheets, Slides, Chat, Forms, Tasks, and Search behind a single OAuth flow. |
| Snowflake-Labs/mcp | New (Beta) | Replaces the earlier snowflakedb/mcp-snowflake-server direction with a Labs-maintained server covering Cortex AI, object management, SQL orchestration, and semantic view querying. |
8. Recent Deprecations
Servers archived, marked end-of-life, or absorbed into a successor since the prior refresh.* You can sort the table by clicking on the column name.
| Server | Status | Successor / Migration |
|---|---|---|
modelcontextprotocol/servers/github | Archived 2025 | Use github/github-mcp-server (official, Go). |
modelcontextprotocol/servers/gdrive | Archived | Use the community taylorwilsdon/google_workspace_mcp (Drive, Calendar, Gmail, Docs, Sheets, Slides, Chat, Forms, Tasks, Search). |
Azure/azure-mcp | Archived 2026-02 | Migrated into the consolidated Microsoft catalog at microsoft/mcp under the Azure.Mcp.Server subdirectory. |
PostHog/mcp | Archived 2026-01 | Moved into the PostHog monorepo at PostHog/posthog/services/mcp. |
googleworkspace/dev-assist, googleworkspace/developer-mcp | Archived 2025-11 | Both first-party Google Workspace MCP repositories were archived in late 2025; the community-maintained taylorwilsdon/google_workspace_mcp is the canonical Workspace MCP server as of this refresh. |
elastic/mcp-server-elasticsearch | Deprecating 2026 | Superseded by the built-in Elastic Agent Builder MCP endpoint in Elastic 9.2 and later; the standalone repository receives only critical security updates. |
modelcontextprotocol/servers/slack | Archived | Use a community fork (e.g. zencoderai/slack-mcp-server) until Slack publishes a first-party server. |
modelcontextprotocol/servers/postgres | Archived | Use crystaldba/postgres-mcp for self-hosted, or AWS Labs aurora-postgres-mcp-server for Aurora. |
modelcontextprotocol/servers/sqlite | Archived | The maintained fork lives under community ownership; many Claude Desktop users now run a local postgres-mcp against an in-memory or socket-backed Postgres instance instead. |
modelcontextprotocol/servers/puppeteer | Archived | Use microsoft/playwright-mcp. |
modelcontextprotocol/servers/brave-search | Archived | Use the first-party brave/brave-search-mcp-server. |
modelcontextprotocol/servers/redis | Archived | Use the first-party redis/mcp-redis. |
modelcontextprotocol/servers/aws-kb-retrieval | Archived | Use AWS Labs bedrock-kb-retrieval-mcp-server. |
| HTTP+SSE transport (spec 2024-11-05) | Deprecated 2025-03-26 | Use Streamable HTTP. Hosts may still connect to legacy HTTP+SSE servers but no new servers should target this transport. |
9. Frequently Asked Questions
9.1 Which transports do most production-grade MCP servers support as of 2026?
The de facto pattern for new servers isstdio+HTTP - the same server binary can run either as a stdio subprocess for local hosts (Claude Desktop, Cursor) or expose a Streamable HTTP endpoint for remote hosts (AgentCore Gateway, Claude Desktop Custom Connectors, Anthropic Messages API). Pure-stdio servers are still common at the reference end of the catalog; pure-Streamable-HTTP servers are typical for vendor-operated remote services. WebSocket is rare and outside the core spec.9.2 Which servers expose Resources or Prompts in addition to Tools?
Resources are most common among reference and vendor servers (filesystem, git, memory, GitHub, AWS Knowledge, Notion, AgentCore Gateway-fronted REST). Prompts are rare across the entire catalog as of 2026 - the reference everything server demonstrates them, and a handful of community servers expose curated review templates, but the majority of servers expose Tools only. If you depend on Resources or Prompts, treat their presence as a per-server claim and verify against the upstream README.9.3 How should I evaluate whether an MCP server is safe to add to Claude Desktop?
The default Claude Desktop trust model treats a stdio MCP server as a local subprocess with full host-user privileges - the same as launching the server binary by hand. Apply the same scrutiny you would for any local CLI: prefer first-party (vendor or reference) maintainers; read the tool list for write or shell-exec tools; for remote servers, require OAuth 2.1 with audience binding and confirm the server's published Protected Resource Metadata; for tools that can write or execute, prefer servers that emitdestructiveHint annotations so the host can prompt before invocation.9.4 Are there OAuth-enabled remote MCP servers I can use without self-hosting?
Yes - the vendor-operated entries in §5 are remote and OAuth-protected. The most often-cited examples in 2026 are GitHub, Cloudflare, Stripe, Atlassian, Notion, and Linear. The Claude Desktop "Custom Connectors" UI installs and authenticates these in one click; the Anthropic Messages API supports them inline via the MCP feature; AgentCore Gateway can be configured to fan them out to multi-tenant agents.9.5 What is the recommended way to fan one MCP server out to multiple agents?
Three idiomatic patterns in 2026:- AgentCore Gateway - route many agents through a single Gateway target that wraps the underlying MCP server. Gateway terminates OAuth 2.1 on the front and assumes a downstream IAM role on the back. Recommended for AWS-native workloads. See AgentCore Implementation Guide Part 4.
- Cloudflare Workers Remote MCP - publish your server as an OAuth-protected Streamable HTTP endpoint on Workers. Recommended for SaaS vendors. Most of the §5.4 servers use this pattern.
- API Gateway + Lambda - the open-source pattern documented in MCP Server on AWS Lambda Complete Guide using AWS SAM, Cognito as the authorization server, and RFC 9728 Protected Resource Metadata. Recommended for AWS-native workloads not running through AgentCore.
10. References
Official spec and reference- modelcontextprotocol.io
- MCP Specification 2025-11-25 (current, first-anniversary release)
- MCP Specification 2025-06-18 (OAuth 2.1 hardening, elicitation)
- MCP Authorization 2025-06-18 (RFC 9728 Protected Resource Metadata, RFC 8707 audience binding)
- MCP Specification 2025-03-26 (Streamable HTTP, tool annotations introduced)
- modelcontextprotocol/servers - reference implementations
- modelcontextprotocol/inspector - MCP testing UI
Vendor catalogs
- AWS Labs MCP catalog
- Amazon Bedrock AgentCore Gateway Developer Guide
- Anthropic - Claude Desktop MCP documentation
- github/github-mcp-server
- Cloudflare Workers Remote MCP documentation
- Stripe MCP documentation
- Atlassian Remote MCP Server
- Notion MCP Server documentation
- Linear MCP Server documentation
- Microsoft MCP catalog (includes consolidated Azure MCP Server under
Azure.Mcp.Server) - Google Workspace MCP (community, MIT)
RFCs referenced in this article
- RFC 8707 - Resource Indicators for OAuth 2.0
- RFC 9728 - OAuth 2.0 Protected Resource Metadata
- RFC 8414 - OAuth 2.0 Authorization Server Metadata
- RFC 7591 - OAuth 2.0 Dynamic Client Registration
Related Articles on This Site
- MCP Server on AWS Lambda Complete Guide
End-to-end pattern for building and shipping a production-grade MCP server on AWS Lambda against the 2025-06-18 spec - Streamable HTTP, OAuth 2.1 with RFC 9728 / RFC 8707, Lambda Function URL streaming, and AgentCore Gateway integration. - Amazon Bedrock AgentCore Implementation Guide Part 1: Runtime, Memory, and Code Interpreter Patterns
The agent runtime that consumes MCP servers like the ones catalogued here. - Amazon Bedrock AgentCore Implementation Guide Part 4: Multi-Agent Orchestration
Supervisor / sub-agent patterns where each sub-agent has its own MCP toolset, and the AgentCore Gateway fan-out pattern that ties them together. - Claude Code Getting Started Guide
The Claude Code host side of the MCP ecosystem - howclaude mcp addwires the servers in this reference into a working agent workflow. - Claude Code Harness and Environment Engineering Guide
The harness-level patterns - settings, hooks, permission gates - that decide which MCP servers are safe to install in a given workspace.
This snapshot is refreshed as needed within the publication year. Last reviewed: 2026-05.
References:
Tech Blog with curated related content
Written by Hidekazu Konishi