AWS History and Timeline regarding AWS CloudFormation - Overview, Functions, Features, Summary of Updates, and Introduction
First Published:
Last Updated:
Table of Contents
- Background and Method of Creating AWS CloudFormation Historical Timeline
- AWS CloudFormation Historical Timeline (Updates from February 25, 2011)
- Current Overview, Functions, Features of AWS CloudFormation
- Frequently Asked Questions
- Summary
This time, I have created a historical timeline for AWS CloudFormation, the Infrastructure as Code (IaC) service that has served as the foundation of AWS deployment automation since February 2011.
AWS CloudFormation predates almost every IaC ecosystem on AWS today. AWS CDK synthesizes into it, AWS SAM is implemented as a transform on top of it, IaC Generator produces templates for it, and Cloud Control API exposes its resource model to other tools. Following its evolution is therefore the most efficient way to understand how the entire AWS IaC ecosystem came to look the way it does.
Just like before, I am summarizing the main features while following the birth of AWS CloudFormation and tracking its feature additions and updates as a Current Overview, Functions, Features of AWS CloudFormation.
I hope these will provide clues as to what has remained the same and what has changed, in addition to the features and concepts of each AWS service.
Background and Method of Creating AWS CloudFormation Historical Timeline
The reason for creating a historical timeline of AWS CloudFormation is that it has quietly become the lowest common denominator of AWS Infrastructure as Code. Whether engineers write AWS CDK in Python or TypeScript, define serverless applications with AWS SAM, deploy multi-account baselines with StackSets, or generate templates from existing resources with the IaC Generator, the underlying execution engine is the same AWS CloudFormation that launched in 2011.Additionally, AWS CloudFormation has been integrated with many surrounding capabilities over the years - Change Sets, Drift Detection, StackSets, Macros, Modules, Custom Resources, Hooks, IaC Generator, Continuous Sync (Git Sync), the Public Registry, and Cloud Control API. Therefore, I wanted to organize the information of AWS CloudFormation with the following approaches.
- Tracking the history of AWS CloudFormation and organizing the transition of updates
- Summarizing the feature list and characteristics of AWS CloudFormation
- Clarifying how related services and tools (AWS CDK, AWS SAM, IaC Generator, Hooks, StackSets, Cloud Control API) connect to AWS CloudFormation as a single ecosystem
There may be slight variations in the dates on the timeline due to differences in the timing of announcements or article postings in the references used.
The content posted is limited to major features related to the current AWS CloudFormation and necessary for the feature list and overview description.
In other words, please note that the items on this timeline are not all updates to AWS CloudFormation features, but are representative updates that I have picked out.
Some dates may shift by a few days depending on the reference used.
In line with the convention used in this Timeline series, this article does not enumerate pricing changes. AWS CloudFormation stack operations on AWS-native resource types are free of charge in themselves; what attracts cost is the resources that the stacks create, and those costs are documented in each underlying service's pricing page rather than in AWS CloudFormation itself.
AWS CloudFormation Historical Timeline (Updates from February 25, 2011)
Now, here is a timeline related to the functions of AWS CloudFormation. As of the time of writing this article, the history of AWS CloudFormation spans about 15 years, with the service having served as the official Infrastructure as Code foundation of AWS since February 2011.2011 | 2012 | 2013 | 2014 | 2015 | 2016 | 2017 | 2018 | 2019 | 2020 | 2021 | 2022 | 2023 | 2024
* The table can be sorted by clicking on the column names.| Date | Summary |
|---|---|
| 2011-02-25 | AWS CloudFormation is announced and made generally available. It introduces a JSON template format with the Resources, Parameters, Outputs, and Mappings sections, the Stack as the management unit, and bootstrap helper scripts (cfn-init, cfn-signal, cfn-hup, cfn-get-metadata) for Amazon EC2 instance bootstrapping. |
| 2011-05-26 | AWS CloudFormation expands to additional regions outside US East. |
| 2011-09-29 | Support for Amazon Virtual Private Cloud (Amazon VPC) resource types. Subnets, route tables, internet gateways, and network ACLs can now be expressed in templates. |
| 2012-04-19 | CloudFormer is announced as a tool to generate templates from existing AWS resources. This is the conceptual ancestor of today's IaC Generator. |
| 2012-09-04 | AWS CloudFormation supports cost estimation through the EstimateTemplateCost API. |
| 2012-12-20 | Stack update support is announced. Templates can be updated in place rather than always requiring a delete-and-recreate cycle. |
| 2013-02-13 | AWS CloudFormation adds support for Amazon RDS Read Replicas. |
| 2013-04-25 | Support for AWS Identity and Access Management (IAM) resources in templates. Users, groups, roles, and managed policies can now be created and managed through AWS CloudFormation. |
| 2013-09-26 | Support for additional resource types and an initial form of Custom Resources via Amazon SNS-backed providers. Users can model arbitrary resources by routing AWS CloudFormation lifecycle events through Amazon SNS to their own handler. |
| 2014-06-17 | Amazon EC2 Container Service (Amazon ECS) resource types are supported in AWS CloudFormation. |
| 2014-11-12 | Amazon CloudWatch Logs resource types are supported. |
| 2014-11-13 | AWS Lambda is announced. Although AWS CloudFormation already supports Amazon SNS-backed Custom Resources, the introduction of AWS Lambda paves the way for a far simpler Custom Resource model in the following months. |
| 2015-04-08 | AWS Lambda becomes usable as a backend for AWS CloudFormation Custom Resources. This is the standard pattern that most teams still use today for filling resource gaps. |
| 2015-04-22 | AWS CloudFormation Designer is announced. Designer is a visual template editor in the AWS Management Console that lets you drag and drop resources and edit the underlying JSON or YAML side by side. |
| 2015-10-07 | AWS CloudFormation introduces WaitConditions with CreationPolicy. A more reliable way to coordinate bootstrap completion than the original WaitCondition / WaitConditionHandle pattern. |
| 2016-03-29 | Change Sets are announced. Operators can preview the exact set of resource-level changes a stack update will produce before applying it. |
| 2016-07-28 | Cross-stack references via Outputs Exports and the Fn::ImportValue intrinsic function are announced. Stacks can now share values without depending on Custom Resources or external parameter stores. |
| 2016-09-19 | YAML template support is announced. Templates can be written in YAML in addition to JSON, with a richer set of short-form intrinsic functions such as !Ref, !Sub, !GetAtt, and !ImportValue. |
| 2016-11-18 | AWS Serverless Application Model (AWS SAM) is announced ahead of AWS re:Invent 2016. AWS SAM is implemented as an AWS CloudFormation Transform (AWS::Serverless-2016-10-31) that expands a compact serverless syntax into a regular AWS CloudFormation template at deployment time. |
| 2017-06-26 | AWS CloudFormation propagates stack-level tags to all supported resource types. This makes tag-based cost allocation and access control across stacks dramatically easier. |
| 2017-07-25 | AWS CloudFormation StackSets is announced. StackSets lets a single template be deployed across many accounts and regions, with administrator-managed permissions and centralized operations. |
| 2018-04-19 | The Drift Detection feature is announced in preview. Stacks can be compared against the actual state of the resources they manage, surfacing out-of-band modifications. |
| 2018-07-17 | AWS Cloud Development Kit (AWS CDK) is announced as a Developer Preview at the AWS Summit in New York. AWS CDK lets engineers describe infrastructure in TypeScript, JavaScript, Python, Java, and C#, then synthesizes a CloudFormation template for actual deployment. |
| 2018-09-05 | CloudFormation Macros are announced. Macros let users register custom Transforms backed by AWS Lambda, so they can extend the AWS CloudFormation template language with team- or product-specific syntactic sugar. |
| 2018-11-13 | Drift Detection becomes generally available. Detection can be invoked on a stack or on individual resources, and the differences are exposed through the console and API. |
| 2019-02-26 | StackSets gains Service-Managed Permissions through AWS Organizations integration. Administrators no longer need to manually create execution roles in every member account. |
| 2019-07-11 | AWS CDK becomes generally available. The General Availability release of AWS CDK marks a turning point in how new AWS workloads are authored, while keeping AWS CloudFormation as the deployment engine underneath. |
| 2019-11-13 | Resource Import is announced. Existing AWS resources can be brought under AWS CloudFormation management without destruction or recreation. |
| 2019-11-18 | The CloudFormation Registry, CloudFormation CLI, and third-party resource support are announced together. Independent software vendors and customers can author resource providers in Java, Python, TypeScript, and Go, register them with the Registry, and use them in templates the same way as AWS-native resource types. |
| 2020-06-16 | AWS CloudFormation Guard is open-sourced and released in preview. Guard is a policy-as-code DSL for validating AWS CloudFormation templates and JSON or YAML configurations at design time. |
| 2020-09-30 | The CloudFormation Registry adds private extension automatic version management. Internal third-party resource types can be managed with a consistent version lifecycle through the Registry. |
| 2020-10-01 | AWS CloudFormation Guard 1.0 becomes generally available. The GA release adds advanced rules with conditions, numeric comparison operators, comment support, and simplified installation through Homebrew and Chocolatey. |
| 2020-10-22 | AWS CloudFormation raises the maximum resources per template to 500 (from 200). Maximum parameters rise to 200 (from 60), mappings to 200 (from 100), and outputs to 200 (from 60), significantly reducing the need for nested stack workarounds. |
| 2020-11-24 | AWS CloudFormation Modules are announced. Modules let teams package reusable groups of resources as first-class AWS CloudFormation types and publish them through the Registry. |
| 2021-05-17 | AWS CloudFormation Guard 2.0 is released. Guard 2.0 is a complete rewrite that generalizes the DSL beyond AWS CloudFormation and expands validation coverage to all template sections, including Description and Parameters. |
| 2021-06-21 | The CloudFormation Public Registry is opened. A new searchable collection of extensions allows customers to discover, provision, and manage third-party resource types, modules, and Hooks published by AWS Partner Network Partners and the developer community. |
| 2021-09-30 | AWS Cloud Control API becomes generally available. Cloud Control API is a uniform CRUDL API for any resource type registered with the CloudFormation Registry, available outside of stacks. |
| 2021-11-17 | AWS CloudFormation Hooks are announced in preview. Hooks let an organization run pre-create, pre-update, and pre-delete validation logic before resource provisioning, enforced as part of the deployment pipeline. |
| 2022-02-10 | AWS CloudFormation Hooks become generally available. GA brings support for stable hook authoring patterns and integration with AWS Config and other governance tooling. |
| 2023-02-09 | AWS CloudFormation introduces support for skipping resources during stack update rollback. Failed updates can be retried without rolling back resources that have already finished updating. |
| 2023-03-22 | AWS CloudFormation StackSets adds support for service-managed deployments with the management account as a target. This closes a long-standing gap in baseline deployments. |
| 2023-09-26 | AWS CloudFormation enables stack refactoring through Resource Import enhancements. Templates can be reorganized without destroying and recreating resources. |
| 2023-11-26 | AWS CloudFormation Git Sync (Continuous Sync) is announced at AWS re:Invent 2023. A stack can be configured to track a Git repository so that pushes to a designated branch automatically deploy as stack updates. |
| 2024-02-05 | AWS CloudFormation IaC Generator becomes generally available. From a list of existing AWS resources in an account, the IaC Generator produces an AWS CloudFormation template that can be used to recreate or import them, including emitting AWS CDK-compatible code paths. |
| 2024-06-26 | AWS CDK adds tighter integration with the IaC Generator output. AWS CDK can ingest IaC Generator templates and convert them into idiomatic AWS CDK code. |
| 2024-09-19 | AWS CloudFormation StackSets adds account filtering and concurrency control improvements. Operations on large multi-account fleets become easier to target and throttle. |
| 2024-12-01 | AWS CloudFormation Hooks gain change set targets, stack-level invocations, and Cloud Control API coverage ahead of AWS re:Invent 2024. Hooks can now run against entire change sets and against stack-level operations, not only against individual resource operations, and managed Hooks for CloudFormation Guard and AWS Lambda are introduced so that AWS-managed policy-as-code rules can be enabled without authoring a custom Hook. |
| 2025-11 | As of late 2025, the AWS CloudFormation ecosystem comprises AWS CloudFormation itself, AWS CDK, AWS SAM, IaC Generator, StackSets, Hooks, Modules, the Public Registry, Cloud Control API, Continuous (Git) Sync, and CloudFormation Guard. This collection forms the de facto Infrastructure as Code stack for AWS workloads. |
This timeline is not exhaustive. New resource type additions, regional expansions, console improvements, and minor quota adjustments are continuous, and have been omitted to keep the table focused on architectural milestones. Where exact public announcement dates were ambiguous between the AWS News Blog and the What's New feed, the entry above reflects the earliest public reference I could correlate. Some dates may shift by a few days depending on the reference used.
Current Overview, Functions, Features of AWS CloudFormation
From here, we will explain in detail the main features of the current AWS CloudFormation.AWS CloudFormation is a declarative Infrastructure as Code service that lets you define a collection of AWS resources as a single template and provision, update, and delete them as a unit called a stack.
AWS CloudFormation streamlines deployment and operation of AWS workloads by treating infrastructure changes as reviewable, repeatable artifacts. It also automatically allocates the resources needed to fulfill the template, performs dependency resolution between resources, and rolls back failed deployments to a known-good state. Through integration with AWS Identity and Access Management (IAM), tagging, and audit trails such as AWS CloudTrail, it offers a security and governance posture consistent with the rest of AWS.
Along with these features, it integrates with surrounding tooling - AWS CDK, AWS SAM, IaC Generator, Hooks, StackSets, Cloud Control API, and the Public Registry - that together form what is commonly referred to as the AWS CloudFormation ecosystem.
AWS CloudFormation Ecosystem
Before diving into the specific features, the following diagram summarizes how the major surrounding components relate to AWS CloudFormation.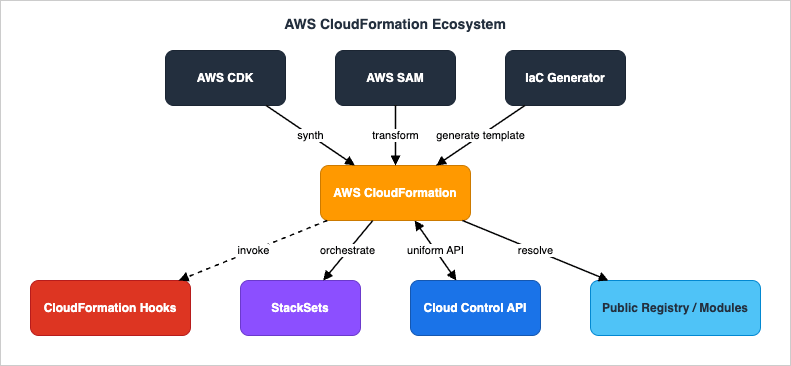
In this diagram, the upper layer (AWS CDK, AWS SAM, IaC Generator) represents authoring and synthesis tools that produce AWS CloudFormation templates. The middle layer is AWS CloudFormation itself, which is the deployment engine. The lower layer (CloudFormation Hooks, StackSets, Cloud Control API, Public Registry / Modules) represents the extension and orchestration layer that AWS CloudFormation invokes, orchestrates, or sources from.
- AWS CDK synthesizes an AWS CloudFormation template from imperative code in TypeScript, Python, Java, and other languages.
- AWS SAM registers itself as an AWS CloudFormation Transform so that compact serverless syntax is expanded into a full AWS CloudFormation template at deploy time.
- IaC Generator inspects existing resources in an account and emits an AWS CloudFormation template (and optionally AWS CDK code) that represents them.
- CloudFormation Hooks are invoked before resource operations to enforce organization-wide policies.
- StackSets orchestrates the same template across many accounts and regions.
- Cloud Control API exposes the AWS CloudFormation resource model as a uniform CRUDL API outside of stacks, enabling third-party tools to drive AWS-native resources through a single API surface.
- Public Registry / Modules stores reusable resource types and module packages that templates can resolve at deploy time.
Core Concepts
AWS CloudFormation models infrastructure with a small, stable set of concepts that have remained largely unchanged since 2011.- Template: A JSON or YAML document that declares the desired state of a set of AWS resources. The top-level sections are
AWSTemplateFormatVersion,Description,Metadata,Parameters,Mappings,Conditions,Transform,Resources, andOutputs. Of these, onlyResourcesis mandatory. - Stack: A running deployment of a template. A stack is the management unit for create, update, and delete operations, and is associated with a status (
CREATE_COMPLETE,UPDATE_ROLLBACK_FAILED, and so on). - Resource: A single managed entity inside a stack, typed by a resource type identifier such as
AWS::S3::BucketorAWS::Lambda::Function. Resource types are versioned and registered with the CloudFormation Registry. - Parameter: A typed input to a template, supplied at stack creation or update time. Parameters can declare allowed values, default values, and constraint descriptions.
- Mapping: A static lookup table inside the template, often used to vary AMI IDs or instance sizes by region or environment.
- Output: A named value exported by a stack, optionally exported with a globally unique name so that other stacks can import it via
Fn::ImportValue. - Change Set: A preview of the resource-level changes that would result from applying a template or parameter update. Change sets surface which resources will be modified in place, replaced, or removed.
Template Authoring (JSON vs YAML, Intrinsic Functions, Conditions, Mappings)
Templates can be authored in either JSON or YAML. YAML became the dominant format after its support landed in 2016, primarily because the short-form intrinsic functions reduce boilerplate and enable comments.Intrinsic functions allow values to be computed at deployment time:
Refresolves to a parameter value or a resource's primary identifier.Fn::GetAttreads an attribute of an existing resource, such asMyBucket.Arn.Fn::Subperforms variable substitution inside a string.Fn::Joinconcatenates values with a separator.Fn::ImportValuereads a value exported by another stack.Fn::FindInMaplooks up a value in aMappingstable.Fn::If,Fn::And,Fn::Or,Fn::Not,Fn::Equalsparticipate in conditional logic.Fn::Length,Fn::ToJsonString, and other newer additions support richer template logic.
dev, staging, and production parameter values and use Conditions to switch between higher-availability and lower-cost configurations.Mappings are simple lookup tables. They are often used for region-keyed values, where the same template needs to choose AMIs, ARN prefixes, or DNS names by region.
Pseudo parameters such as
AWS::AccountId, AWS::Region, AWS::StackName, and AWS::Partition are populated automatically by AWS CloudFormation at deploy time.Custom Resources (Lambda-backed)
Custom Resources are the supported mechanism for filling in gaps where a native AWS CloudFormation resource type does not exist or where additional orchestration is needed (for example, performing a one-time SaaS configuration step as part of a deployment).A Custom Resource is declared with
AWS::CloudFormation::CustomResource (or the shorthand Custom::<Name>) and is wired to an AWS Lambda function (or, less commonly, an Amazon SNS topic) that receives Create, Update, and Delete lifecycle events.The handler is expected to:
- Read the event payload to determine the lifecycle operation.
- Perform the side effect required.
- Send a response back to a pre-signed Amazon S3 URL provided in the event, with
Status: SUCCESSorStatus: FAILEDand any outputDatato be exposed viaFn::GetAtt.
us-east-1 (such as an AWS Certificate Manager certificate) while the rest of the stack lives in another region, AWS Lambda-backed Custom Resources are the canonical way to bridge the gap.For a deeper walkthrough of cross-region deployment using Custom Resources, see Deploy AWS CloudFormation Stack Cross-Region with AWS Lambda Custom Resources and AWS CloudFormation Templates and AWS Lambda Custom Resources for Associating AWS Certificate Manager, Lambda@Edge, and AWS WAF with a Website on Amazon S3 and Amazon CloudFront Cross-Region.
Nested Stacks and Modules
There are two complementary mechanisms for composing AWS CloudFormation templates into larger units.Nested Stacks use the
AWS::CloudFormation::Stack resource type to declare another stack as a resource inside the parent stack. The nested stack template is fetched from an Amazon S3 URL at deploy time, and its outputs are accessible via Fn::GetAtt.Nested stacks are well suited to splitting large architectures into logical layers (networking, security, applications) so that each layer can be developed and reviewed in isolation, while still being deployed together.
Modules, introduced in 2020, are a more recent and more declarative composition mechanism. A Module is published to the CloudFormation Registry and is referenced in a template the same way a regular resource type is. The Module's contents are inlined into the consuming template at deploy time, which means there is no nested stack to manage and no separate quotas to track.
Modules are recommended when the same group of resources is reused across many templates and the goal is to centralize their definition. Nested stacks remain a better fit when each child needs its own independent lifecycle.
StackSets (Self-Managed / Service-Managed, Account Filter, Auto-Deployment)
AWS CloudFormation StackSets is the multi-account, multi-region deployment layer on top of AWS CloudFormation. A single template is published as a StackSet, and individual stack instances are created in selected accounts and regions.There are two permission models.
- Self-Managed Permissions: Administrators manually create an administration role in the management account and an execution role in every target account. This is the original model and is still used for accounts that are not part of AWS Organizations.
- Service-Managed Permissions: With AWS Organizations integration, the roles are managed automatically. StackSets can target the entire organization, specific organizational units (OUs), or filtered subsets.
- Account filters to include or exclude specific accounts within an OU.
- Automatic deployment to new accounts as they are added to the targeted OU.
- Concurrent operations with configurable concurrency to avoid overwhelming any single account.
- Drift detection at the StackSet level to surface accounts whose stack instances have diverged.
Drift Detection
Drift Detection compares the current state of a stack's managed resources against the configuration the stack believes them to have. When a resource is modified outside of AWS CloudFormation - for example, an operator edits a security group rule in the console - drift detection surfaces the difference.Drift detection can be initiated from the AWS Management Console, the AWS CLI (
detect-stack-drift, detect-stack-resource-drift), and the AWS SDK. Results are exposed at three independent levels:- Stack level (
StackDriftStatus):DRIFTED,IN_SYNC,UNKNOWN, orNOT_CHECKED. - Resource level (
StackResourceDriftStatus):IN_SYNC,MODIFIED,DELETED, orNOT_CHECKED. - Property level (
PropertyDifferenceType):ADD(a value has been added to a property that is an array or list),REMOVE(a property has been removed from the current configuration), orNOT_EQUAL(the current property value differs from its expected value).
StackSets supports drift detection at the StackSet level, which fans out the operation to every stack instance and aggregates the result for the administrator.
Macros and Transforms (SAM Transform, Include Transform)
CloudFormation Macros and Transforms are how the template language is extended at deploy time.A Transform is declared at the top level of a template (
Transform: AWS::Serverless-2016-10-31 for AWS SAM, for instance). Before any resources are provisioned, the Transform processes the template and produces an expanded version. The Transform implementation is an AWS Lambda function registered with AWS CloudFormation.The two AWS-provided Transforms most commonly seen are:
AWS::Serverless-2016-10-31(the AWS SAM Transform): Expands compactAWS::Serverless::Functionand related types into full AWS CloudFormation resources.AWS::Include: Substitutes content from another file located in Amazon S3 into the template at the point of declaration.
Macros are powerful but should be treated with care: because they run at deploy time and can rewrite the template body, they are a security-sensitive surface. Reviewers and consumers need to trust the Macro publisher, and operators should pin Macro versions when reproducibility matters.
CloudFormation Hooks (Public Extensions, Private Hooks, Cloud Control API)
CloudFormation Hooks were announced in preview in 2021 and reached general availability in February 2022. Hooks let an organization run policy-as-code checks before an AWS CloudFormation operation actually provisions resources.A Hook is registered with the CloudFormation Registry like any other extension. It declares which resource types it targets and which lifecycle phases it should intercept (
PRE_CREATE, PRE_UPDATE, PRE_DELETE). When AWS CloudFormation processes a change set or stack operation, it invokes each applicable Hook in sequence, and a FAIL result aborts the operation.Two deployment models are supported:
- Public Hooks: Published in the Public Registry. Examples include AWS-provided guardrails such as enforcing encryption on
AWS::S3::Bucketresources. - Private Hooks: Registered to a specific account or to an AWS Organization. These are the typical fit for company-internal guardrails (for example, "no public Amazon S3 buckets in this OU").
Late in 2024, Hooks were extended in two further ways. First, the target surface expanded from individual resource operations to change set targets and stack-level invocations, so that a Hook can validate the overall shape of a deployment - not just one resource at a time. Second, AWS introduced managed Hooks for CloudFormation Guard and AWS Lambda, which let teams enable AWS-authored policy-as-code rules through a managed extension instead of authoring and operating a custom Hook from scratch.
IaC Generator (Generate-from-Resources)
The IaC Generator, which became generally available in February 2024, addresses one of the longest-standing gaps in AWS CloudFormation: importing resources that were not originally created through a stack.The workflow is:
- The IaC Generator scans an account for resources of supported types.
- The user selects a subset of those resources and groups them into a logical template.
- The IaC Generator produces an AWS CloudFormation template (and optionally AWS CDK code) representing those resources.
- The template can be imported into a new or existing stack via the Resource Import feature, bringing the resources under AWS CloudFormation management.
The IaC Generator does not address every resource type and does not always produce idiomatic templates: complex resources with circular dependencies or implicit configuration may need manual cleanup after generation. Treat the output as a starting point that captures the structural truth, not as a finished artifact.
Continuous Sync / Git Sync
Announced at AWS re:Invent 2023 and rolled out through late 2023 and 2024, AWS CloudFormation Git Sync allows a stack to track a Git repository (initially supporting AWS CodeCommit, GitHub, GitLab, and Bitbucket through AWS CodeConnections).When a designated branch is updated and the change resolves to a valid template path, AWS CloudFormation creates a change set automatically and (depending on the sync configuration) either applies it or waits for an explicit approval. The end result is that the desired state of a stack is described in version control as the single source of truth, and the deployment loop closes without an external CI/CD pipeline.
For teams that already operate a mature CI/CD pipeline, Git Sync is not a replacement; it is a useful option for environments where a full pipeline is overkill - for example, the long tail of small bookkeeping stacks per team or per environment.
Relationship to CDK and SAM
The presence of AWS CDK and AWS SAM does not replace AWS CloudFormation; both ultimately produce AWS CloudFormation templates that the CloudFormation service deploys.- AWS CDK is a synthesis-time abstraction. AWS CDK code in TypeScript, Python, Java, C#, or Go is executed by the CDK CLI, which emits an AWS CloudFormation template into the
cdk.out/directory. The CDK CLI then drives AWS CloudFormation deployments and reads AWS CloudFormation's status. The mental model that helps most users is: AWS CDK is a typed template generator; AWS CloudFormation is the deployment engine. - AWS SAM is a deploy-time abstraction. An AWS SAM template is an AWS CloudFormation template that uses the
AWS::Serverless-2016-10-31Transform. The AWS SAM CLI invokes AWS CloudFormation, which applies the Transform to expand the compact serverless syntax into the full set of resources (AWS Lambda function, AWS IAM role, Amazon API Gateway, event sources, and so on).
For a side-by-side comparison of AWS CloudFormation, AWS CDK, AWS SAM, and Terraform - including state management and migration patterns - see Comparing Terraform, AWS CDK, AWS SAM, and CloudFormation - A Practitioner's Guide to Mental Models, State Management, and Migration.
Cloud Control API and Public Registry
Two additional ecosystem surfaces are worth understanding because they exist alongside AWS CloudFormation rather than inside it.Cloud Control API is a uniform CRUDL (Create, Read, Update, List, Delete) API for any resource type registered with the CloudFormation Registry. Whereas the AWS CloudFormation service operates on stacks (groups of resources), Cloud Control API operates on individual resources. The same resource provider that handles an
AWS::S3::Bucket inside an AWS CloudFormation stack also handles it when called through Cloud Control API.This matters because it lets external IaC tools (Terraform, Pulumi, Crossplane, and others) drive AWS-native resources through a single, generic API surface, while still benefiting from the AWS CloudFormation governance pipeline (including Hooks).
The Public Registry is the catalog of public extensions: third-party resource types, modules, and Hooks. Vendors and customers can publish their own extensions and consume others'. Modules in particular are an effective way to package and version reusable groups of resources without forking templates.
Used together, Cloud Control API and the Public Registry effectively turn AWS CloudFormation into a federated control plane for AWS-native resource lifecycle management, rather than a deployment-only service.
Frequently Asked Questions about AWS CloudFormation History
The following are short answers to common questions about the AWS CloudFormation history.When did AWS CloudFormation launch?
AWS CloudFormation became generally available on February 25, 2011. It launched alongside the bootstrap helper scripts (
cfn-init, cfn-signal, cfn-hup, cfn-get-metadata) and supported the original JSON template format.When did Custom Resources launch?
The first generation of Custom Resources, backed by Amazon SNS, was announced in September 2013 as part of broader template language enhancements. The far more widely used AWS Lambda-backed Custom Resources became available on April 8, 2015, shortly after AWS Lambda itself reached general availability.
When did StackSets launch?
AWS CloudFormation StackSets was announced on July 25, 2017. Service-Managed Permissions through AWS Organizations integration followed on February 26, 2019.
When did Drift Detection launch?
Drift Detection was announced in preview on April 19, 2018, and reached general availability on November 13, 2018.
When did AWS CDK and AWS SAM launch, and how do they relate to AWS CloudFormation?
AWS SAM was announced on November 18, 2016, ahead of AWS re:Invent 2016. It is implemented as the AWS CloudFormation Transform
AWS::Serverless-2016-10-31, which means an AWS SAM template is processed by AWS CloudFormation itself at deploy time. AWS CDK was announced as a Developer Preview on July 17, 2018, at the AWS Summit in New York, and became generally available on July 11, 2019. AWS CDK is a synthesis-time tool: it produces an AWS CloudFormation template that AWS CloudFormation then deploys.When did Macros and Modules launch?
CloudFormation Macros were announced on September 5, 2018, allowing user-defined AWS Lambda-backed Transforms. CloudFormation Modules followed on November 24, 2020, as a more declarative way to package reusable groups of resources and publish them through the CloudFormation Registry.
When did CloudFormation Hooks launch?
CloudFormation Hooks were announced in preview on November 17, 2021, and reached general availability on February 10, 2022. Hooks provide pre-create, pre-update, and pre-delete policy enforcement that also applies to Cloud Control API operations.
When did the IaC Generator launch?
AWS CloudFormation IaC Generator became generally available on February 5, 2024. It generates AWS CloudFormation templates (and optionally AWS CDK code) from existing AWS resources in an account, lowering the barrier to bringing organically grown environments under Infrastructure as Code management.
When did Continuous Sync (Git Sync) launch?
AWS CloudFormation Git Sync was announced at AWS re:Invent 2023 on November 26, 2023. Stacks can be configured to track a Git repository so that pushes to a designated branch result in automatic change sets or deployments.
Summary
In this article, I created a timeline of the history of AWS CloudFormation to see how its functions, role, and surrounding ecosystem have changed over the years.AWS CloudFormation began in 2011 as a relatively narrow service: a JSON template language, a
cfn-init-based bootstrap pattern, and a small initial catalog of resource types. What is remarkable looking back is how stable the core mental model has remained. Templates, stacks, parameters, outputs, intrinsic functions, and resources still mean what they meant in 2011. Almost every subsequent feature, from Change Sets to StackSets to Hooks to the IaC Generator, can be understood as an extension of that core vocabulary rather than a replacement for it.That stability is the reason a parallel ecosystem of authoring tools could grow on top of it. AWS CDK chose to be a synthesis-time abstraction precisely because it could trust the AWS CloudFormation template format to remain a durable interchange representation. AWS SAM chose to be a Transform precisely because the Transform mechanism was already a first-class feature of the template language. The IaC Generator could be added in 2024 because the resource provider model standardized in 2018 made it possible to reverse-engineer existing resources back into a template.
The 2017 to 2024 stretch is where the surrounding ecosystem accelerated most: StackSets (2017), AWS CDK Developer Preview (2018), CloudFormation Macros (2018), Drift Detection (2018), the CloudFormation Registry (2019), Modules (2020), Cloud Control API (2021), Hooks GA (2022), Git Sync (2023), and IaC Generator (2024). The result is that AWS CloudFormation is no longer "just" an Infrastructure as Code service; it is the substrate that the rest of AWS Infrastructure as Code depends on.
I am continuously impressed with the disciplined, backwards-compatible evolution of AWS CloudFormation, which has become an indispensable service when using AWS. I am eager to see what new ecosystem features (more deeply integrated generative AI authoring, richer Hook semantics, broader Cloud Control coverage) AWS CloudFormation will introduce in the future. I plan to keep updating this article's timeline regularly to keep a close watch on it.
Also, there is a timeline for the entire history of AWS services, including services other than AWS CloudFormation. Please take a look if you are interested.
AWS History and Timeline - Almost All AWS Services List, Announcements, General Availability(GA)
References:
AWS Documentation(AWS CloudFormation User Guide)
AWS Documentation(Document history for the AWS CloudFormation User Guide)
AWS Documentation(AWS CloudFormation Command Line Interface)
AWS Documentation(AWS Cloud Development Kit (AWS CDK) v2 Developer Guide)
AWS Documentation(AWS Serverless Application Model (AWS SAM) Developer Guide)
AWS Documentation(AWS Cloud Control API User Guide)
AWS Documentation(CloudFormation Hooks)
AWS Documentation(CloudFormation Git sync)
AWS Documentation(IaC Generator)
What's New with AWS?
AWS News Blog
AWS DevOps and Developer Productivity Blog
References:
Tech Blog with curated related content
Written by Hidekazu Konishi